Alleged 13-Million Philippine Data Leak Emerges, Retail and Payment Ecosystem Under Investigation
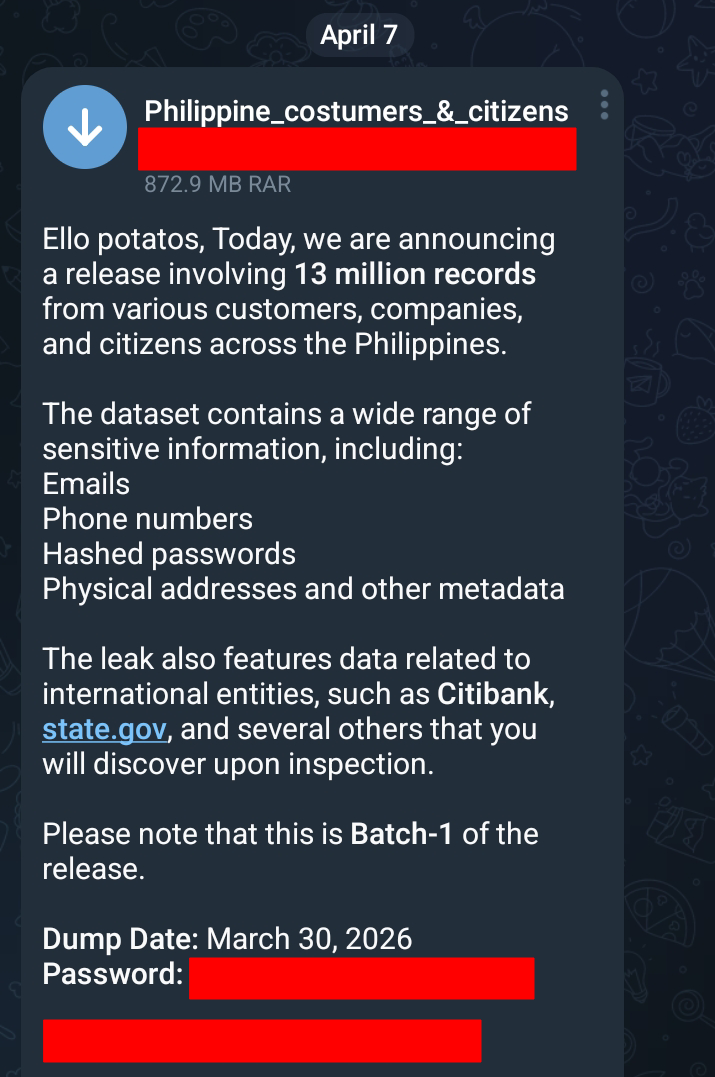
A large-scale alleged data breach involving millions of Filipino records has surfaced online, based on circulating screenshots and dataset previews attributed to a group identifying itself as “FEMBOYSec.” The dataset suggests that approximately 13 million records tied to customers, companies, and citizens across the Philippines may have been exposed, raising concerns across both the retail and digital payments sectors. The dataset, labeled “Philippine_customers_&_citizens_data,” appears to have been distributed as a compressed archive of around 872 MB, which reportedly expands to more than 5.5 GB once extracted. The release is described by the threat actor as “Batch-1,” indicating the possibility of additional data dumps in the near future.
https://iili.io/BGiw4ZF.png
Based on the available information, the dataset allegedly contains a wide range of sensitive information, including email addresses, phone numbers, hashed passwords, physical addresses, and other forms of metadata. The presence of structured directories and database-like naming conventions suggests that the data may have been extracted from backend systems rather than scraped from public sources. Additionally, the threat actor claims that the dataset includes records linked to international entities, referencing financial and government-related domains, although these claims have not yet been independently verified.
Initial technical validation of the exposed files reveals a directory structure consistent with enterprise-level data storage, particularly those used in e-commerce and retail operations. Several folders appear to contain customer details, helpdesk conversations, order information, membership records, and audit logs. Notably, multiple entries reference database tables commonly associated with Magento, an open-source e-commerce platform widely used by businesses to manage online stores, customer accounts, and transactions. The inclusion of tables such as customer entities, sales orders, and address records strongly suggests that the source of the data may be tied to a compromised web application backend or improperly secured database environment.
Early analysis also points to a possible connection with Landers Superstore, based on dataset labels and file naming patterns such as “landers.data” and membership-related records. Landers is a membership-based retail warehouse chain in the Philippines that operates both physical stores and online services, relying heavily on customer databases, purchase histories, and integrated payment systems. While these indicators provide an initial direction for investigation, it is important to emphasize that this connection remains unconfirmed and requires further validation before any definitive attribution can be made.
The potential involvement of Landers also brings attention to its established relationship with Maya, formerly known as PayMaya. Landers has partnered with Maya for digital payment solutions, including QR-based transactions and co-branded financial products such as membership-linked credit cards. This integration highlights a broader ecosystem where customer identity data, transaction records, and payment metadata may intersect across platforms. At this time, there is no evidence indicating that Maya itself has been directly compromised; however, the connection is relevant in understanding how data may flow between interconnected systems and how a breach in one platform could have wider implications.
Further examination of the dataset structure indicates that the exposed information may have originated from a centralized system managing multiple operational components, including customer relationship management (CRM), order processing, and internal communications. The inclusion of helpdesk conversation logs and audit-related data suggests that the breach, if confirmed, may extend beyond basic customer information and into internal business operations. This type of exposure could provide threat actors with deeper insights into system architecture, workflows, and user behavior, potentially enabling more targeted attacks in the future.
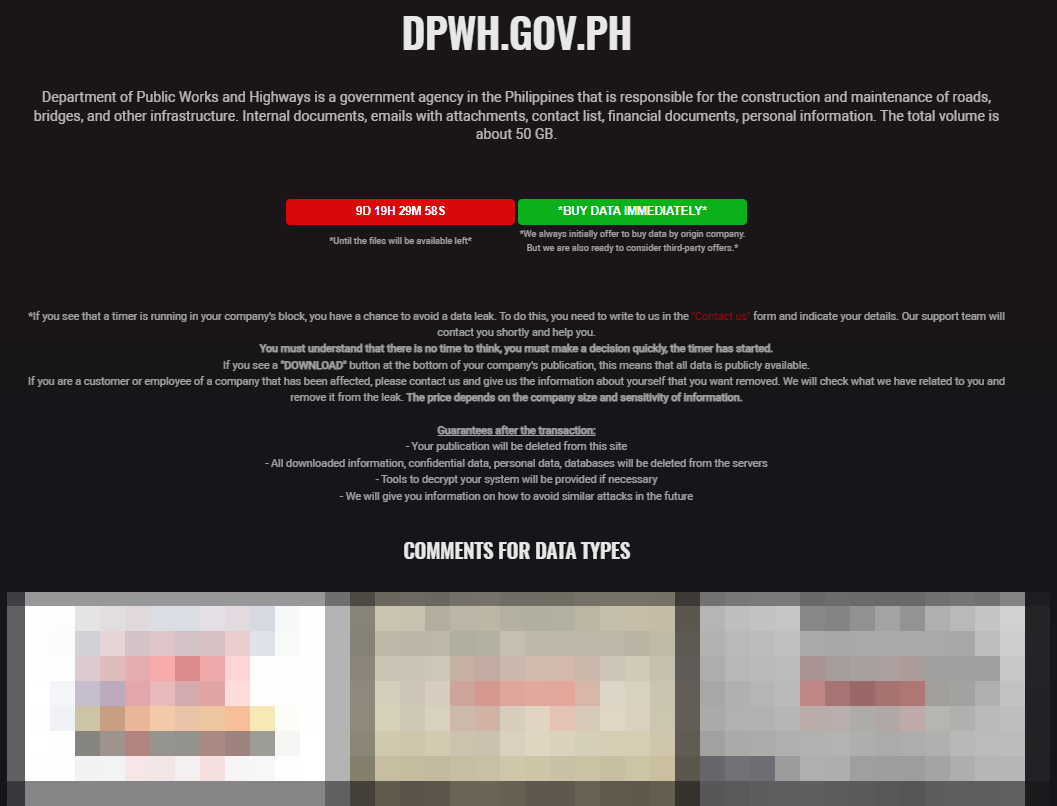
At present, the authenticity and full scope of the dataset remain under investigation. While the structure and content appear consistent with legitimate enterprise data exports, independent verification is still ongoing. No official statements have been issued by the entities potentially involved, and it remains unclear how the data was obtained, whether through exploitation of a system vulnerability, credential compromise, or misconfigured storage.